Host Reputation
In the Censys Platform, hosts are assigned a reputation score that describes whether they are benign or malicious. This score enables you to prioritize alerts with IP indicators faster and perform triage and analysis more effectively with a transparent and consistent scoring methodology.
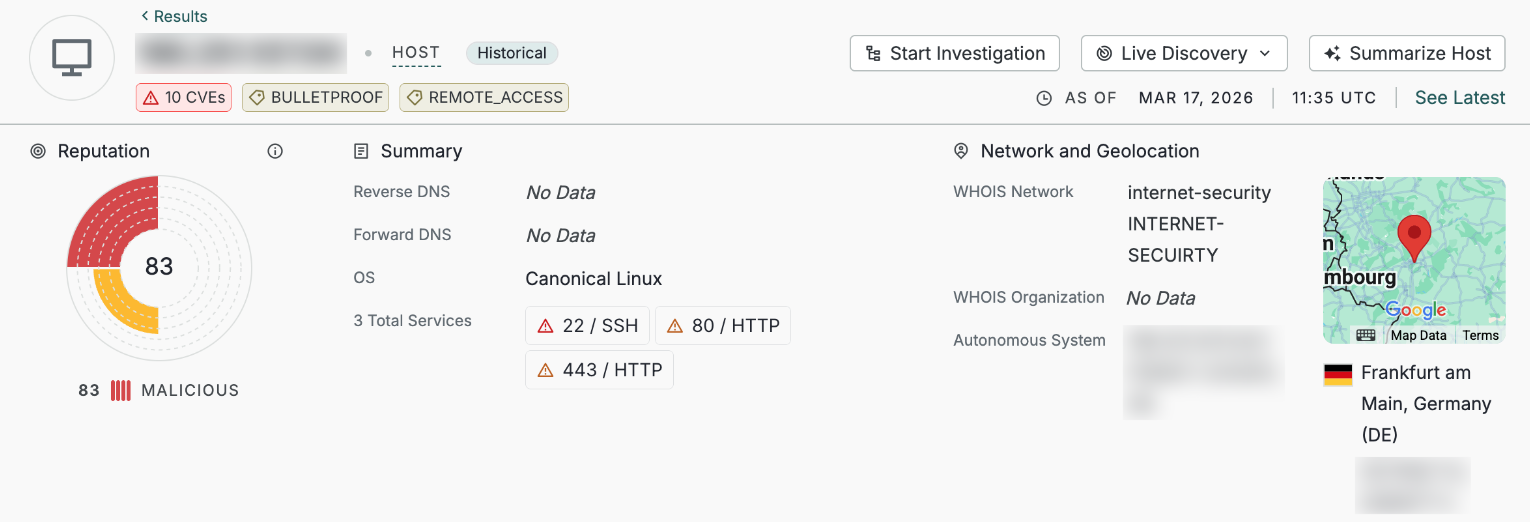
An example host and its reputation score shown in the Platform UI.
Reputation scores and their attendant data are only available to Censys Enterprise users. Additional score context data is available to Censys Enterprise users with access to the Adversary Investigation module. See the entitlement table below for more information.
Video overview
Score details and data
Hosts are assigned a score ranging from 0 (benign) to 100 (malicious). This score is visible on host preview and detail cards in the Platform web UI and is present in the host.reputation data object for searching across in the UI or API.
Ranges for each reputation score level are described below.
| Score | Level |
|---|---|
| 0-20 | Benign |
| 21-40 | Low Risk |
| 41-60 | Medium Risk |
| 61-80 | High Risk |
| 81-100 | Malicious |
Reputation scores are determined based on the following criteria.
Category | Description |
|---|---|
Command and control (C2) and offensive tooling infrastructure | Whether tools associated with C2 or offensive operations were detected on a host. This is one of the strongest indicators of malicious intent in Censys methodology. Examples include hosts running known malicious tools like AsyncRAT, Cobalt Strike, and so on. |
Phishing, impersonation, and deceptive infrastructure | Represents infrastructure used for user deception or impersonation. This strongly influences a host's reputation score. Examples include hosts running Gophish and fake captcha services. |
Network infrastructure | Indicates infrastructure that tolerates or enables persistent malicious activity. This is a structural signal but is not determinative on its own. Examples include hosts associated with "bulletproof" hosting services. |
Anonymization infrastructure | Provides contextual information about traffic obfuscation or identity masking. This signal does not imply malicious intent in isolation and is weighted lower in Censys methodology. IPinfo VPN, privacy, and Tor detections help determine whether anonymization infrastructure is present on a host. |
Reputation score criteria weighting and formula
The weighting system is structured to ensure that any asset identified with a single, validated threat signal, such as an active phishing domain, is immediately classified in the High Risk (61-80) or Malicious (81-100) categories in the user interface.
For example, when a confirmed threat matches a primary risk factor like the presence of offensive tooling, the calculation is designed to result in a sufficiently high score (in the range of 81 or higher) to accurately reflect its true severity.
The formula for determining a reputation score is as follows.
- The values for
phishing_impersonation_and_deceptive_activity,network_infra, andanonymization_infrawill be0if the signal is not present. The value will be1if the signal is present. - Values for
command_and_control_and_offensive_toolingcan be the following:1if a threat or C2 tool was present in the Censys scans of the host within the past 7 days.0.75if a threat or C2 tool was observed by Censys scans in the from 7 to 30 days.0.5if a threat or C2 tool was observed by Censys scans from 30 to 60 days.0if a threat or C2 has not been observed by Censys scans or was present over 60 days ago.
Reputation score = ((command_and_control_and_offensive_tooling * 0.82) + (phishing_impersonation_and_deceptive_activity * 0.82) + (network_infra * 0.42) + (anonymization_infra * 0.42)) x 100While the raw calculation for an asset that matches multiple categories could potentially result in a score above 100 (such as 124), the final Reputation Score is capped at 100 to ensure it remains within the 0-100 range.
Reputation score in the UI
A host's reputation score is shown on search result cards and on the host details page.
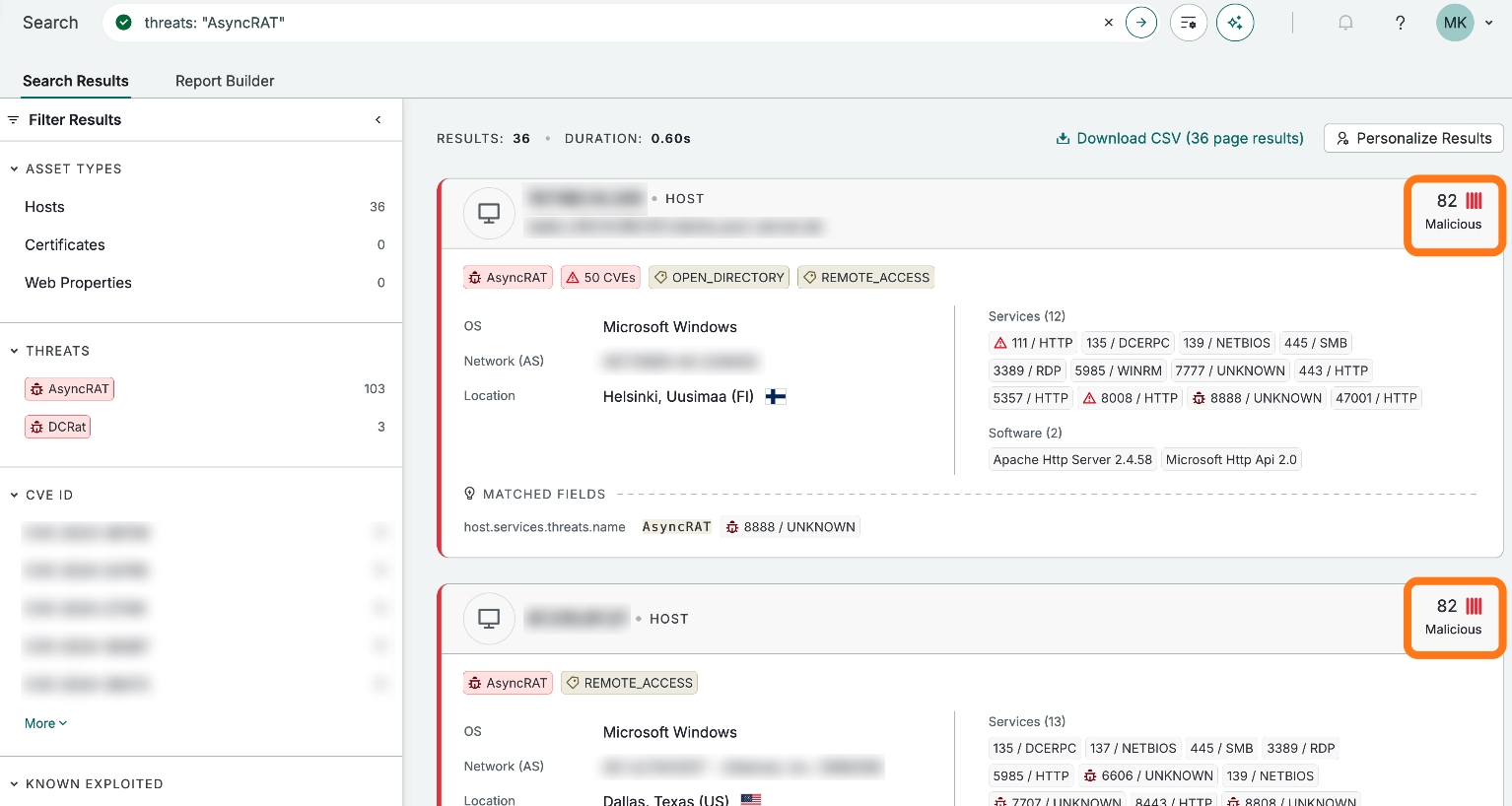
Reputation scores on host preview cards.
On host detail cards, click the Reputation tab to see additional detail about the asset's score, including the evidence categories used to determine the host's score and the host data associated with each category.
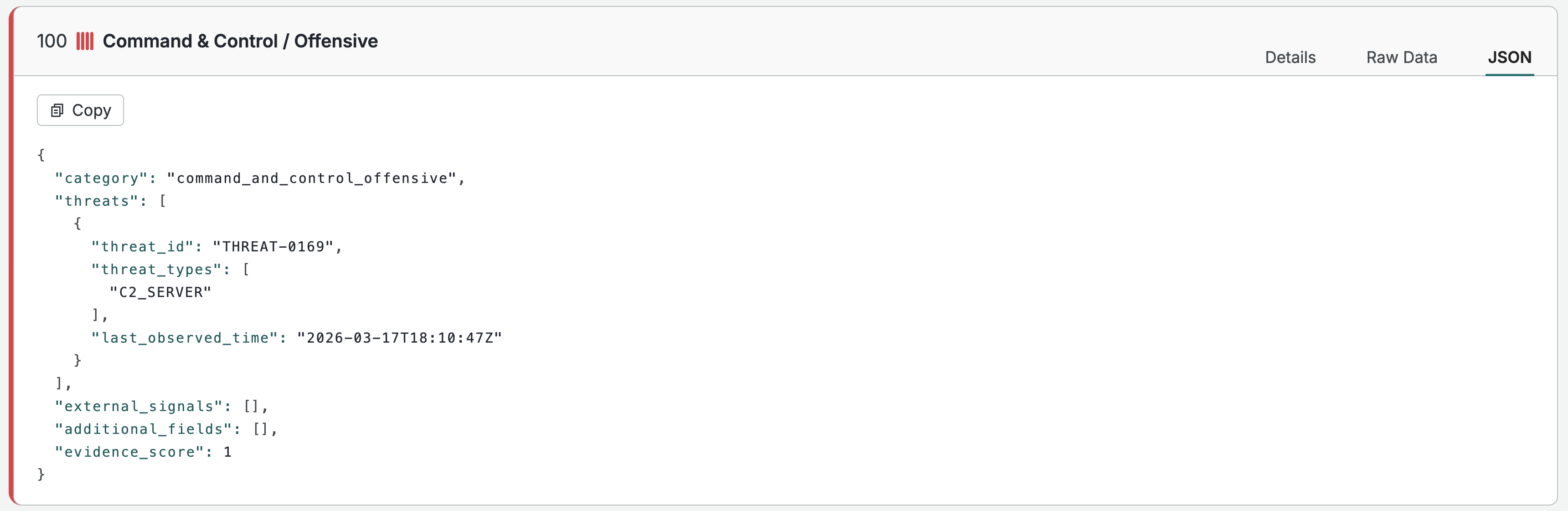
The JSON view of evidence for the command and control category on an example host.
Reputation score data
Reputation score data can be searched across in the UI or retrieved via API by targeting the host.reputation object. Note that score values are floating integers containing up to three decimal places. A reputation score of 81 in the UI is represented in the data as 0.81.
Reputation score data availability
The following table describes which data fields are available to different user entitlement levels.
| Data group | Censys Search | Censys Enterprise | Censys Enterprise with Adversary Investigation module |
|---|---|---|---|
Reputation score and level (host.reputation.score and host.reputation.score.level) | No - can see that a host has a reputation score, but not its value | Yes | Yes |
Category scores (host.reputation.evidence.evidence_score) | No | Yes | Yes |
Evidence summary (host.reputation.evidence.category) | No | Yes | Yes |
Full evidence (including nested host.reputation.evidence.threats data) | No | No | Yes |
Historical reputation score data
Historical reputation score data is not available. On historical hosts, the reputation score shown in the raw data is the reputation score based on the most recent scan data. It is not reflective of the reputation score of the host at a particular point in time.
Updated 3 days ago