Summary
- New
twistfunction for Platform search queries. - Added matched services for search results in the Platform UI and API.
- New fingerprints for popular KVM products and Ollama.
- One Rapid Response bulletin for an RCE in Cisco IOS and IOS XE software.
Platform
-
Use the new
twistfunction in your Platform queries to find field values that are similar to a specified value.- You can use the
twistfunction to find typosquatted domains or domains attempting to impersonate a valid domain by omitting known domains from your query. For example, the following query will find web properties that use names similar tocensys.iobut will omit results that includecensys.io.* * twist(web.hostname, 'censys.io') and not web.hostname:'censys.io'
- You can use the
-
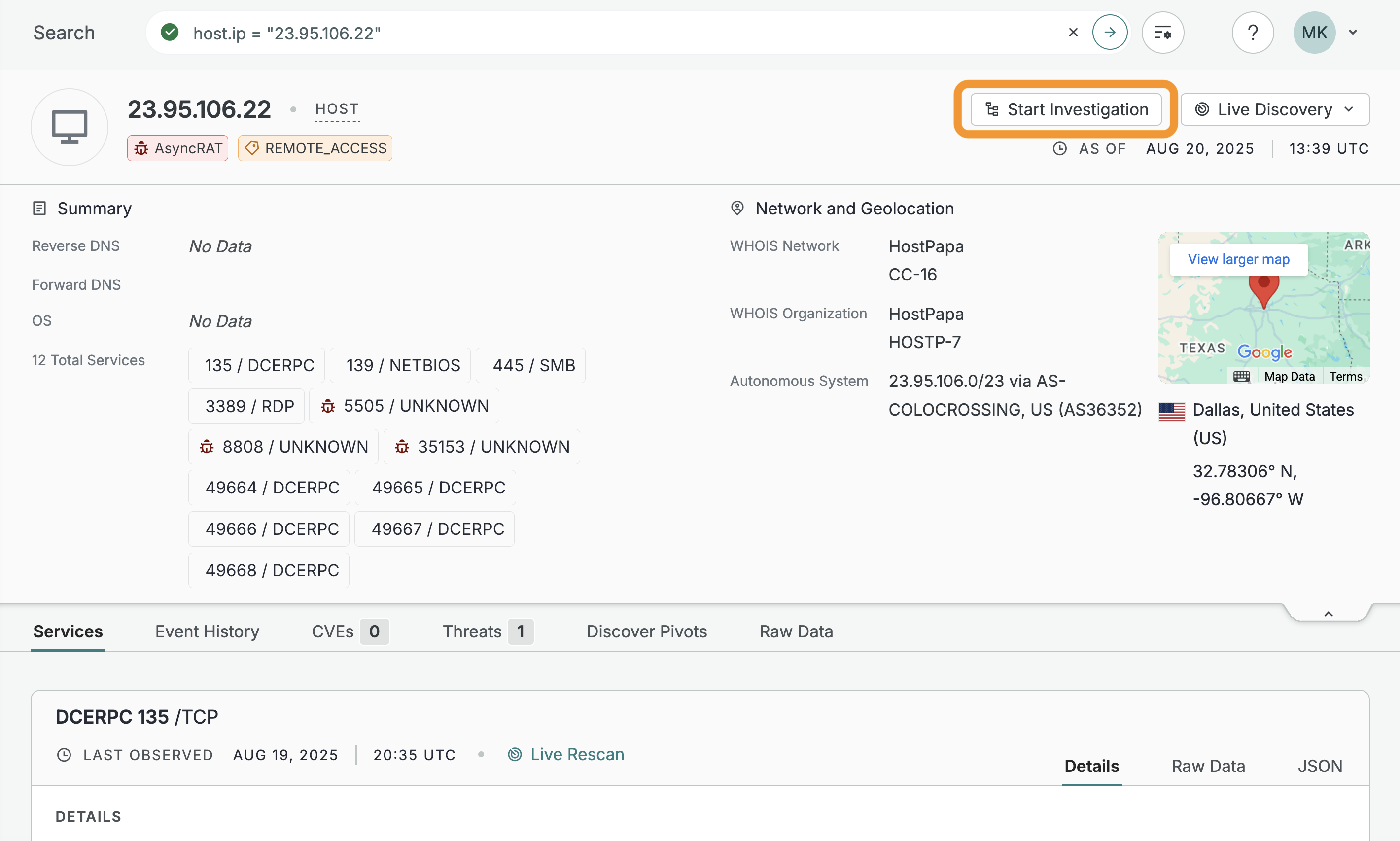
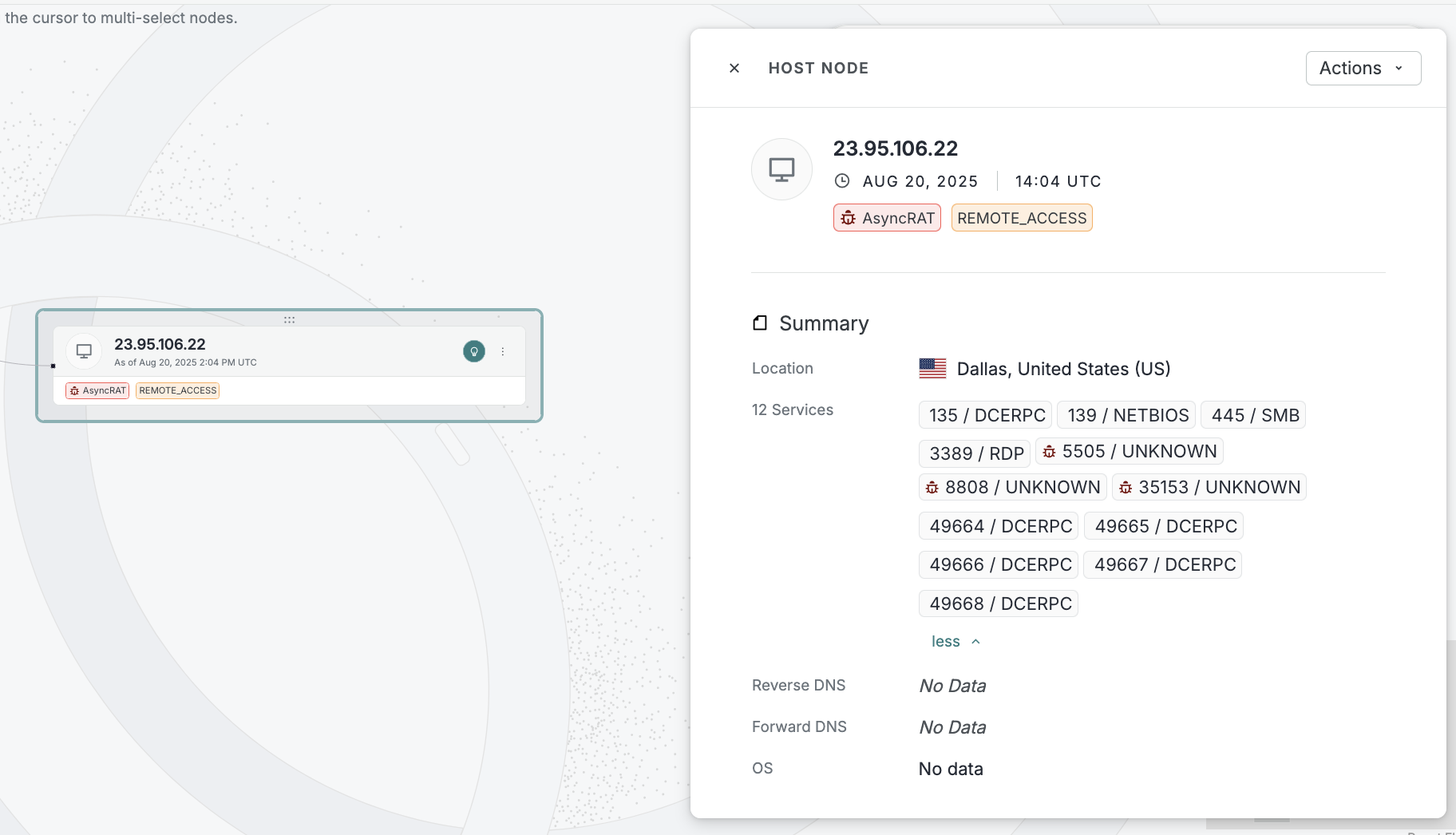
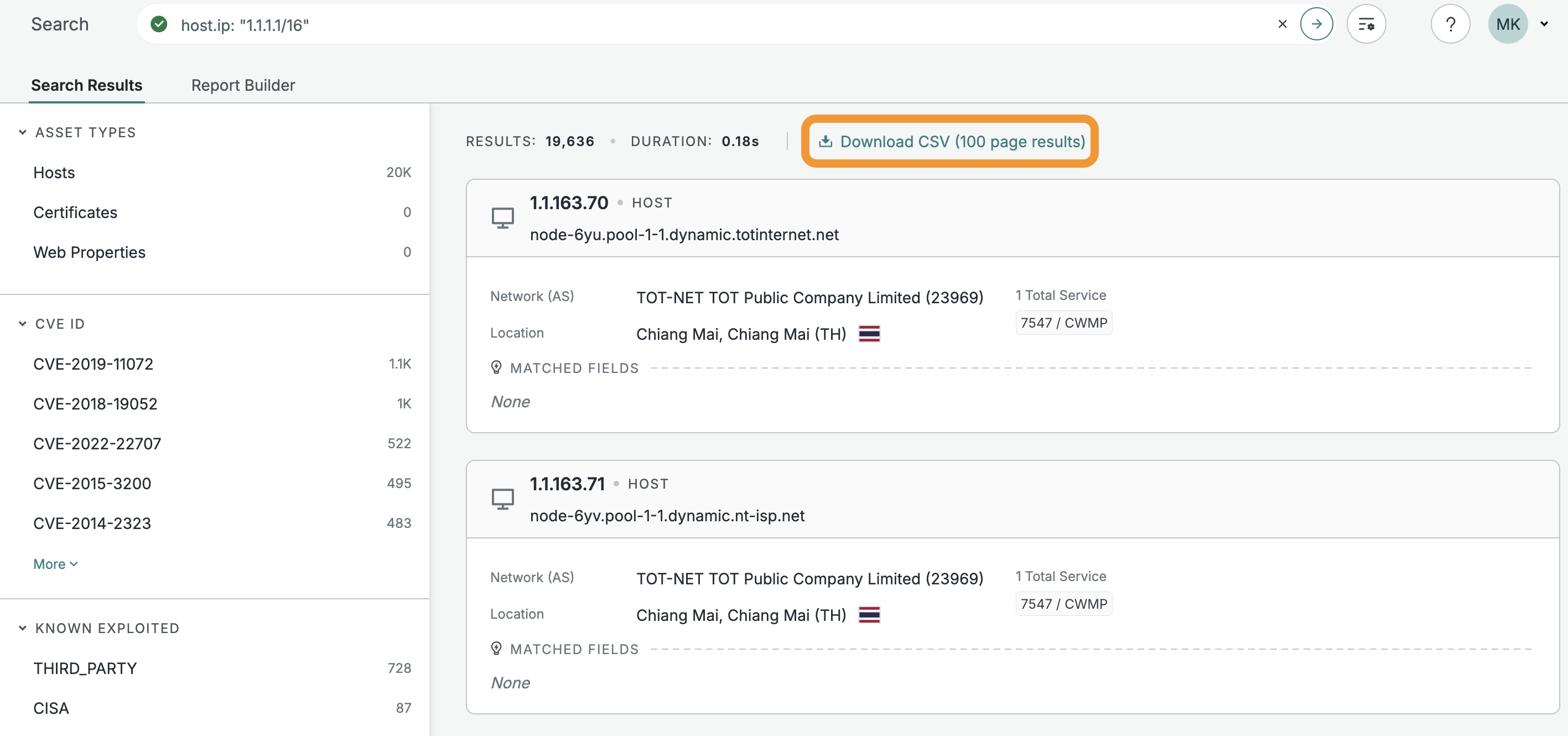
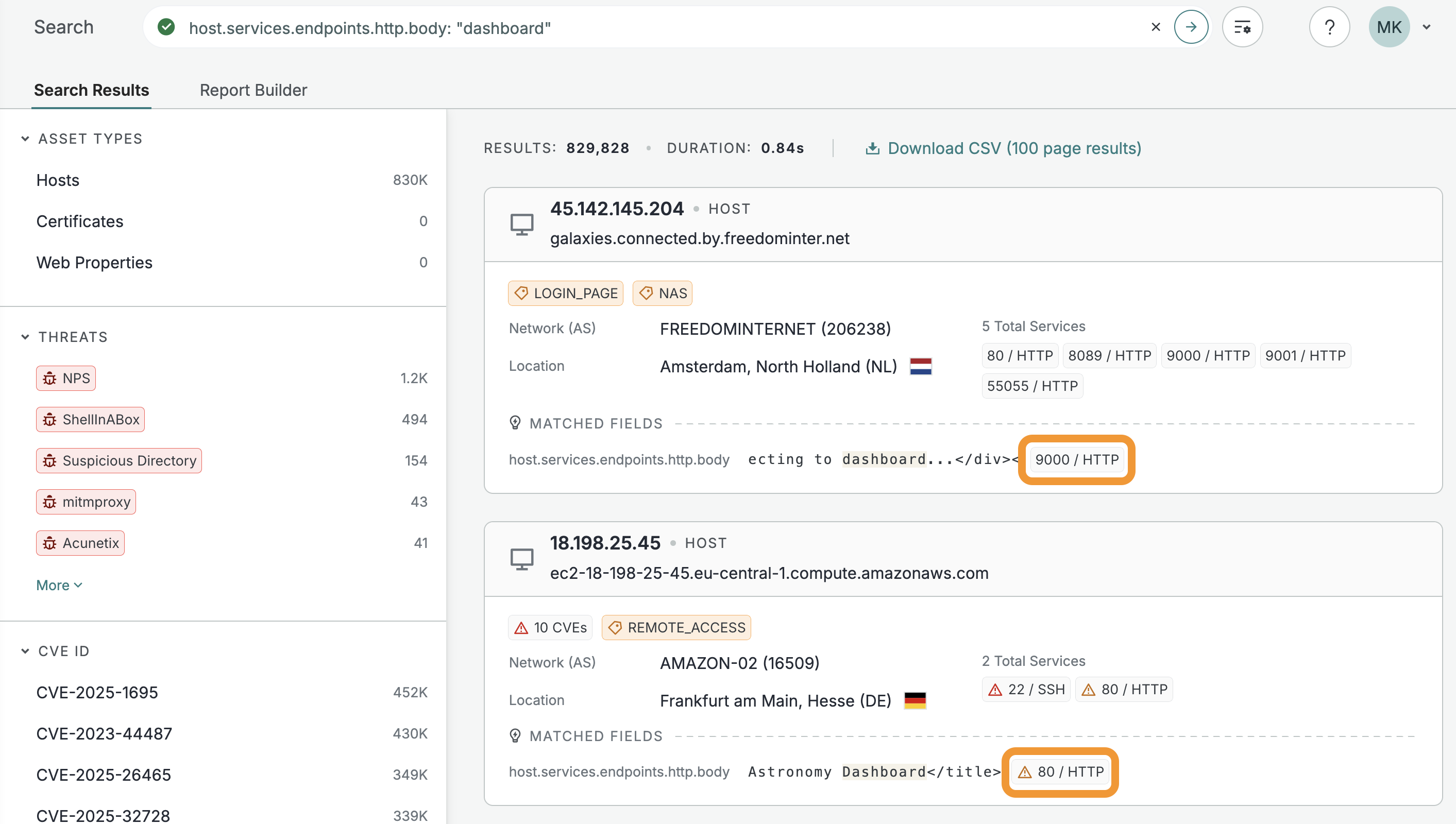
Use matched services in the UI and API to rapidly find host services that contain data that match your search criteria.
-
Matched services in the UI are shown in the Matched Fields section. Click the service icon to navigate directly to the service card on the host.
-
Matched services in the API are returned in a
matched_servicesobject for each host that contains matching data."matched_services": [ { "protocol": "HTTP", "port": 18083, "transport_protocol": "tcp" } ]
-
-
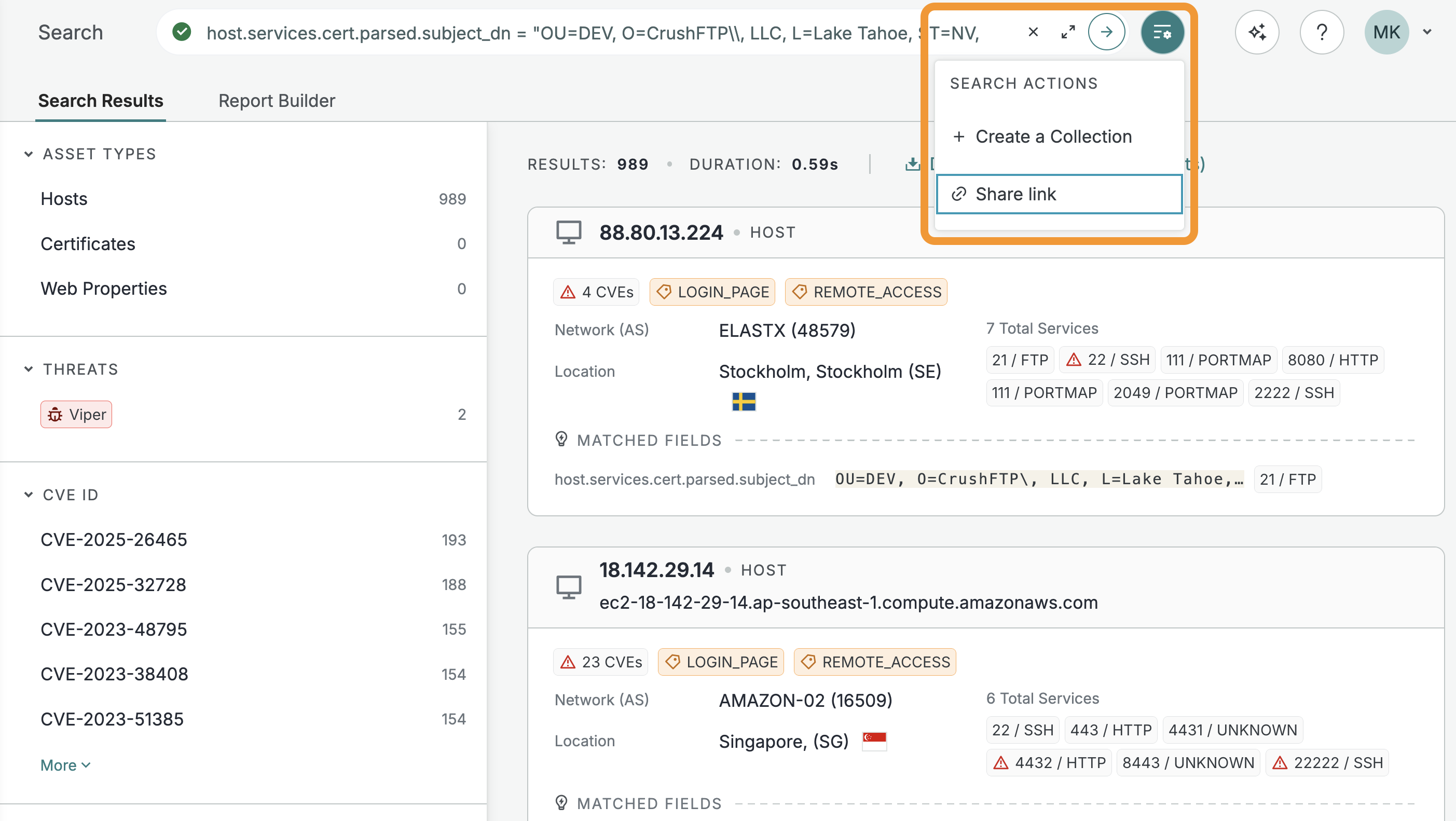
The Share link action was moved to the Search Actions menu next to the search bar in the Platform web UI. Use this to generate share links for assets, search query results, and more.
Rapid Response
The Censys Rapid Response team published information about and queries for the following issue.
-
SNMP RCE in Cisco IOS and IOS XE Software [CVE‑2025‑20352]
- The queries below can help identify any affected Cisco devices exposing SNMP, but they are not necessarily vulnerable.
New fingerprints
Added the following fingerprints.
| Type | Name | Query |
|---|---|---|
| software | NanoKVM | Platform query |
| software | TinyPilot KVM | Platform query |
| software | JetKVM | Platform query |
| software | PiKVM | Platform query |
| software | BliKVM | Platform query |
| software | EJOIN SMS Gateway/SimBox | Platform query |
| software | Ollama AI Model Hosting Platform | Platform query |
| software | Palo Alto Networks Cortex XSOAR EDL Service | Platform query |