February 2, 2026
Summary
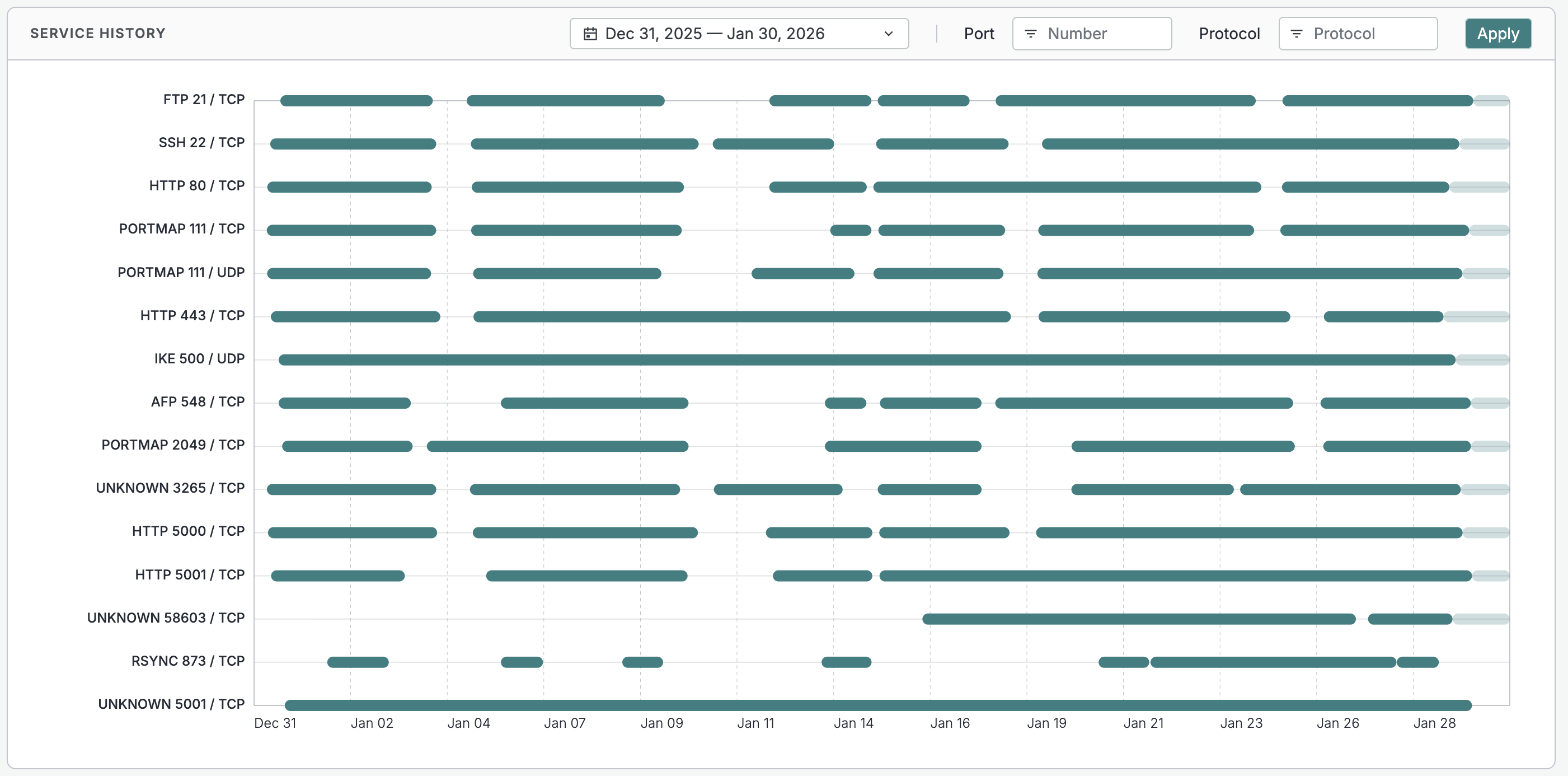
- Use the new Service History timeline on host records in the Platform to quickly understand service history, persistence, anomalies, and other points of interest.
- Use new HTTP redirect data in the Platform to identify misconfigurations, relationships, and more.
- You can now use the Censys Assistant to quickly generate human-readable summaries of certificates and web properties in the Platform web UI.
- Version 1.0 of the
cencliPlatform command line tool was released. It includes more usefulshortoutputs,orgcommands for organization details, and support for streaming output. - Added new risk fingerprints for exposed OpenClaw interfaces, exposed EIP services, exposed CODESYS services, exposed MCP inspector services, and SmarterMail instances vulnerable to CVE-2026-23760 to ASM.
- Added one new software fingerprint for OpenClaw.
Platform
-
The new Service History timeline on host records is a visualization of service presence over time broken down by protocol and port pairs. Use it to quickly understand service history, persistence, anomalies, and other points of interest.
-
Added several parsed data fields for HTTP redirect chains to hosts and web properties.
-
Use this data to map relationships, identify misconfigurations, find parked domains, locate abandoned infrastructure, and more. For example, run
web.endpoints.http.redirect_chain.hostname="censys.com"to find web properties that redirect tocensys.com. -
Redirect data is provided in the following fields.
Field Description [host.services or web].endpoints.http.redirect_chainThe nested object that contains redirect chain data. *.endpoints.http.redirect_chain.reasonThe reason for the redirect. Can be HTTP_3XX,REFRESH_HEADER, orUNRECOGNIZED.*.endpoints.http.redirect_chain.transport_protocolThe transport protocol used for the redirect. *.endpoints.http.redirect_chain.hostnameThe hostname that the redirect points to. *.endpoints.http.redirect_chain.pathThe path that the redirect points to, like /,/login,/admin, and so on.*.endpoints.http.redirect_chain.portThe port that the redirect points to. -
Redirect data is visible to and searchable by users on the Core and Enterprise plans. Redirect data is visible to Starter and Free users, but they cannot search across it.
-
-
You can now use the Censys Assistant to quickly generate human-readable summaries of certificates and web properties in the Platform web UI.
-
Version 1.0 of the
cenclicommand line tool was released. It includes:- The option to retrieve informative and concise
shortoutputs for numerous commands. - New
orgcommands to view organization details including credits, members, and organization information. - Support for streaming output, allowing you to fetch large amounts of data without performance issues.
- The option to retrieve informative and concise
New fingerprints
Added the following fingerprints.
Note that new ASM risk fingerprints may be disabled in your workspace. Reference your risk type configuration in the ASM web console to review new risk types.
Type | Name | Description | Query |
|---|---|---|---|
software | OpenClaw Interface | OpenClaw (formerly Clawdbot/Moltbot) is an open-source personal AI assistant that can execute commands, automate tasks, and manage workflows on the host system. | Platform query |
risk | Exposed OpenClaw Interface | An OpenClaw control interface is exposed to the internet. OpenClaw (formerly Clawdbot/Moltbot) is an open-source personal AI assistant that can automate tasks on the host system. Exposing this interface may allow unauthorized access to execute arbitrary commands and access sensitive data. | ASM risk query: |
risk | EIP (EtherNet/IP) Service Exposed | This service is running EtherNet/IP (EIP), an industrial communication protocol for PLCs, HMIs, and industrial automation equipment. Exposure could allow attackers to read/write PLC programs, modify control logic, disrupt industrial processes, or cause equipment damage. | ASM risk query: |
risk | CODESYS Service Exposed | This service is running CODESYS, an automation platform for industrial control systems. Exposure could allow attackers to read/write PLC programs, modify control logic, disrupt industrial processes, or cause equipment damage. | ASM risk query: |
risk | Exposed MCP Inspector | Exposed MCP Inspector instance. This is a visual developer tool for testing and debugging Model Context Protocol servers. | ASM risk query: |
risk | Vulnerable SmarterMail [CVE-2026-23760] | This SmarterMail server is running a build version vulnerable to CVE-2026-23760, a critical authentication bypass vulnerability that allows unauthenticated attackers to reset administrator accounts without verifying credentials or reset tokens. Since SmarterMail administrator privileges include the ability to execute operating system commands, successful exploitation results in complete administrative compromise with SYSTEM or root-level access on the underlying host. Build versions 9510 and earlier are vulnerable. | ASM risk query: |