May 11, 2026
Summary
- You can now use tags and comments on assets in the Censys Platform to categorize, track, and collaborate on investigations.
- Quickly understand domain-to-host relationships, analyze infrastructure changes over time, and review extensive DNS records using Censys Active DNS.
- New endpoint hash observation history API endpoint for Adversary Investigation module users.
- Two new Censys ARC Rapid Response advisories.
- Added three new fingerprints and two new risks for ASM.
Platform
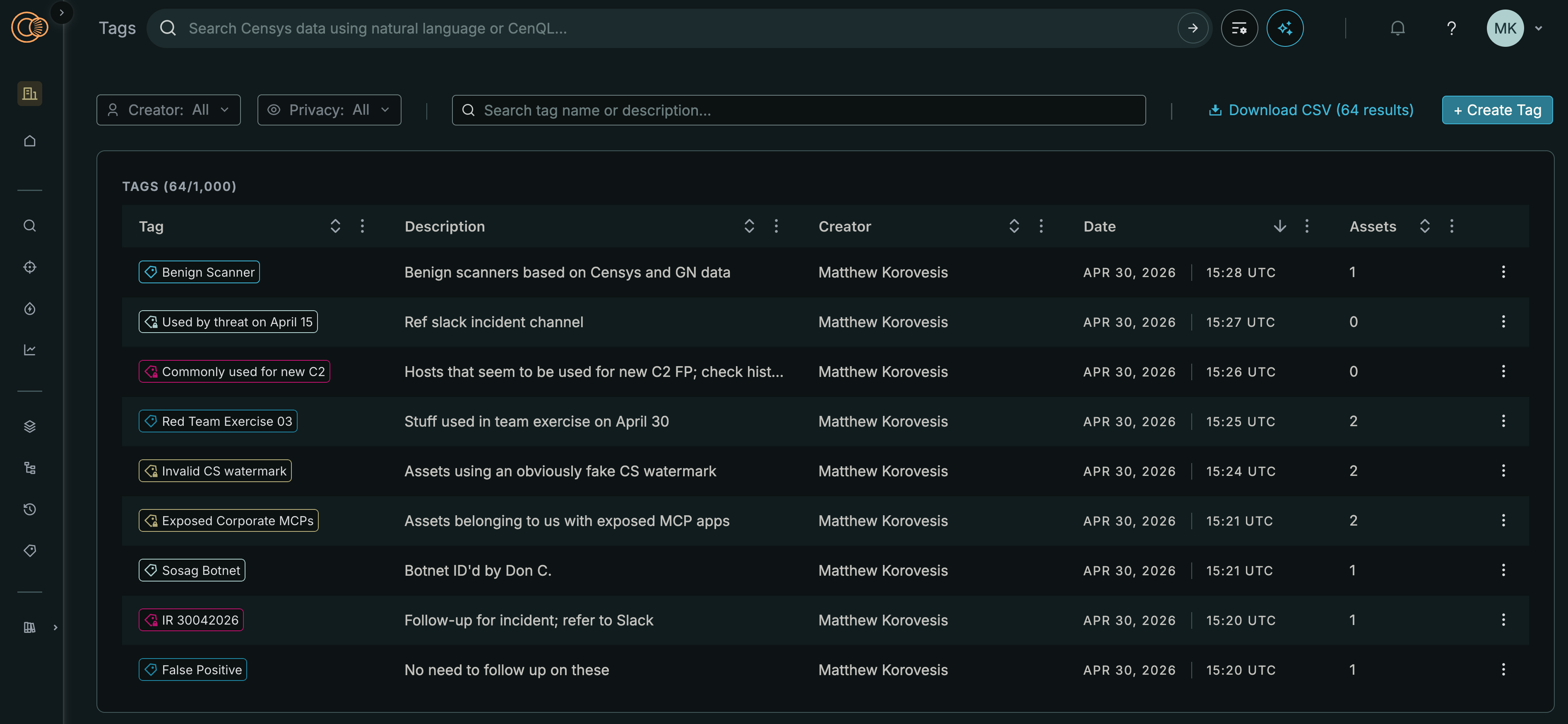
- You can apply custom tags and comments to assets in the Censys Platform for categorization, reference, review, and many other purposes.
- Tags can also be managed via the API.
- Tags and comments are available to users on Censys Starter, Censys Search, and Censys Enterprise plans.
- Quickly understand domain-to-host relationships, analyze infrastructure changes over time, and review extensive DNS records using Censys Active DNS.
- You can use Censys Active DNS to:
- View current and historical A, AAAA, CNAME, MX, NS, SOA, and TXT records for a domain. Records are resolved directly by Censys approximately every 24 hours.
- Analyze domain infrastructure changes and timelines. See exactly when a domain changed from one IP or another, how long it persisted, and what ran there.
- Instantly pivot from any domain to its host IP, open services, threats, certificates, and more. You can also pivot in the other direction from a host IP to see all domains that have ever been present on it.
- Active DNS is a beta feature available to Censys Enterprise customers.
- You can use Censys Active DNS to:
Adversary Investigation
- Use the get endpoint observation history for a host API endpoint to retrieve historical endpoint-level hash observations for a host.
- This action returns time frames during which Censys observed host service endpoint body, favicon, and banner hash values.
Censys ARC Rapid Response
The Censys ARC team published information about the following issues.
- May 5 Advisory: Progress MOVEit Automation Authentication Bypass [CVE-2026-4670]
-
May 7 Advisory: Palo Alto PAN-OS User-ID Authentication Portal Buffer Overflow [CVE-2026-0300]
- The following queries can be used to identify exposed instances. Not all of these services are necessarily vulnerable.
New fingerprints and risks
Added the following fingerprints.
Note that new ASM risk fingerprints may be disabled by default in your workspace. Reference your risk type configuration in the ASM web console to review new risk types.
New fingerprints
| Name | Description | Query |
|---|---|---|
| OpenEMR | This is an OpenEMR electronic health record and practice management application, used by clinics and healthcare organizations for clinical documentation and patient care workflows. | Platform query |
| MetInfo CMS | MetInfo is an open-source content management system (CMS). | Platform query |
| FRITZ!Box | FRITZ!Boxes are residential gateway devices. | Platform query |
New risks
Name | Description | Query |
|---|---|---|
Vulnerable n8n [CVE-2026-42233] | This service is running a vulnerable version of n8n affected by CVE-2026-42233, a critical SQL injection flaw in the Oracle Database node select operation. Unsanitized Limit-field input can alter SQL queries and expose data from connected Oracle databases. | |
Vulnerable Apache HTTP Server [CVE-2026-23918] | The affected Apache HTTP Server is running a version potentially vulnerable to CVE-2026-23918, a double free in the HTTP/2 protocol handler triggered on early connection reset. On servers with HTTP/2 enabled, this may allow a remote attacker to achieve remote code execution. | |